SECURE/TEST DATA LAYER
Data Management Framework
Challenges
01
Not Recognizing the data
- Data scattered in different source systems
- Lack of ownership on data fields within the organization.
- The lack of traceability of data integrated within the organization.
02
Data Validity & Consistency
- Maintaining the format of live data.
- Ensuring integrity.
- Validity and Consistency.
03
Customer Satisfaction
- Loss of Reputation
- Loss of Customer
- Loss of Income
- Customer Distrust

04
Storage Cost
- Managing large volume of data
- Define relationship
- Increased storage cost
05
Development Cost
- Huge time cost
- Managing different systems and Technologies.
- Reuseability
- Performance
06
Governance & Regulation
- Enterprise Data Governance Structure
- Compliance with Regulation (GDPR, KVKK)
- Financial penalties
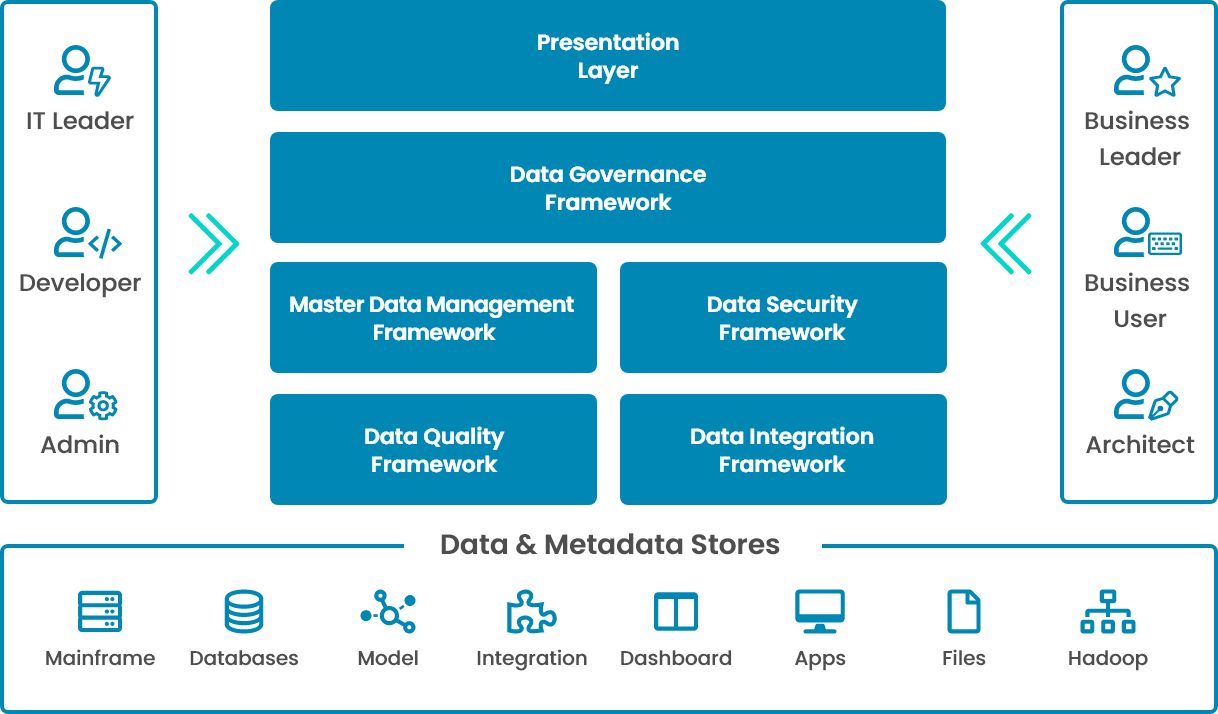
What is Secure/Test Data Layer?
It is a Data Security Framework for;
- Pre-built Connectors such as Relation Databases, Applications and Big Data etc.
- Sensitive Data Discovery and Classification
- Relational Data Subset
- Persistent Data Masking
- Performance and Scability
- Monitoring and Management (Schedule etc.)
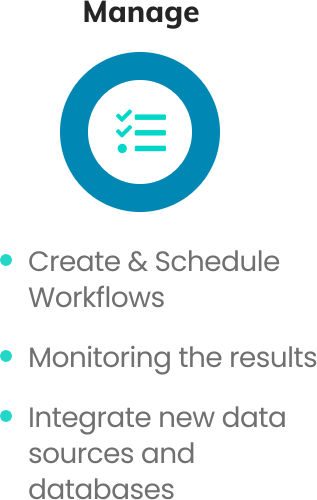
High Level Architecture
What it is Key Benefits?
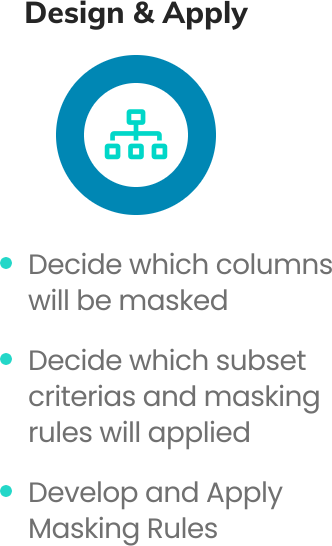
Secure / Test Data Layer Approach